- Главная
- Разное
- Бизнес и предпринимательство
- Образование
- Развлечения
- Государство
- Спорт
- Графика
- Культурология
- Еда и кулинария
- Лингвистика
- Религиоведение
- Черчение
- Физкультура
- ИЗО
- Психология
- Социология
- Английский язык
- Астрономия
- Алгебра
- Биология
- География
- Геометрия
- Детские презентации
- Информатика
- История
- Литература
- Маркетинг
- Математика
- Медицина
- Менеджмент
- Музыка
- МХК
- Немецкий язык
- ОБЖ
- Обществознание
- Окружающий мир
- Педагогика
- Русский язык
- Технология
- Физика
- Философия
- Химия
- Шаблоны, картинки для презентаций
- Экология
- Экономика
- Юриспруденция
Что такое findslide.org?
FindSlide.org - это сайт презентаций, докладов, шаблонов в формате PowerPoint.
Обратная связь
Email: Нажмите что бы посмотреть
Презентация на тему Hacker techniques, tools, and incident handling. (Chapter 1)
Содержание
- 2. Learning ObjectiveExplore the history and current state
- 3. Key ConceptsBirth and evolution of hacking1960s: individuals
- 4. Types of Hackers Script kiddies are
- 5. TAP Principle of ControlsTechnical: software/hardware such as
- 6. Hacker Motives MonetaryFinancial gainsStatusGaining recognitionTerrorismScare, intimidate,
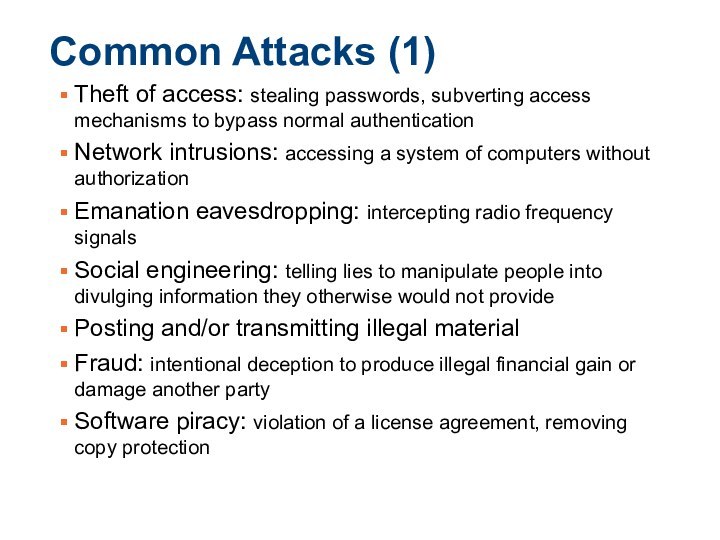
- 7. Common Attacks (1)Theft of access: stealing passwords,
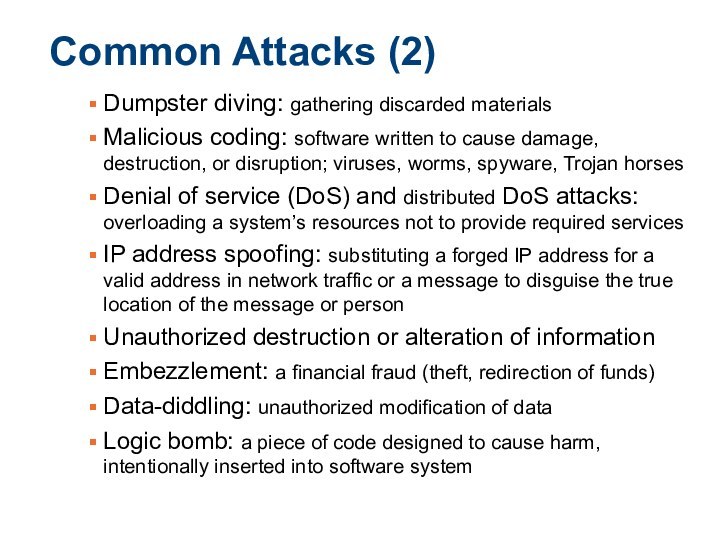
- 8. Common Attacks (2)Dumpster diving: gathering discarded materials
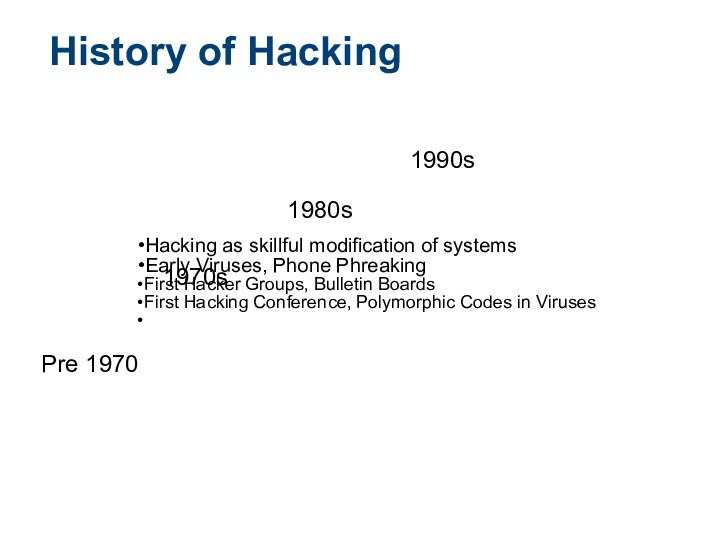
- 9. Hacking as skillful modification of systemsEarly Viruses,
- 10. Famous Hacks over Time1988 Robert T. Morris:
- 11. Famous Hackers and GroupsIndividual Hackers: Kevin Poulsen,
- 12. Modern Hacking and CybercriminalsTransformation of hobbyist hacking
- 13. Ethical Hacking and Penetration TestingEthical hackers require
- 14. Key Points about Ethical HackingIt requires explicit
- 15. C-I-A Triad
- 16. C-I-A TriadConfidentiality: safeguarding information or services against
- 17. Common Hacking Methodologies
- 18. Hacking MethodologiesFootprinting: An attacker passively acquires information
- 19. Penetration Testing Flow
- 20. Performing a Penetration TestNext logical step beyond
- 21. Laws and Ethical StandardsEthical hackers should exercise
- 22. Скачать презентацию
- 23. Похожие презентации
Learning ObjectiveExplore the history and current state of hacking and penetration testing, including their ethical and legal implications.





Слайд 3
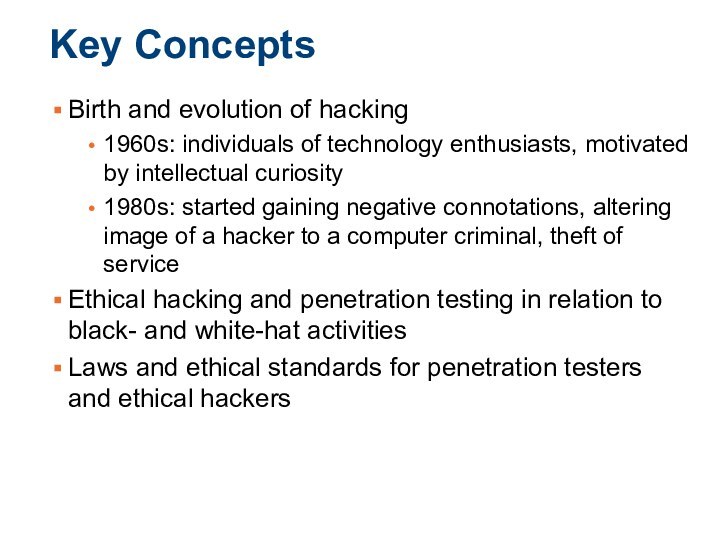
Key Concepts
Birth and evolution of hacking
1960s: individuals of
technology enthusiasts, motivated by intellectual curiosity
1980s: started gaining negative
connotations, altering image of a hacker to a computer criminal, theft of serviceEthical hacking and penetration testing in relation to black- and white-hat activities
Laws and ethical standards for penetration testers and ethical hackers
Слайд 4
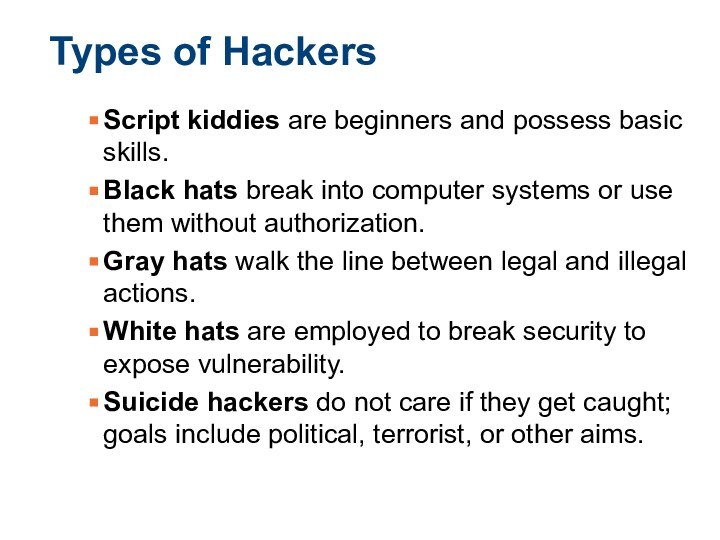
Types of Hackers
Script kiddies are beginners and possess
basic skills.
Black hats break into computer systems or use
them without authorization.Gray hats walk the line between legal and illegal actions.
White hats are employed to break security to expose vulnerability.
Suicide hackers do not care if they get caught; goals include political, terrorist, or other aims.
Слайд 5
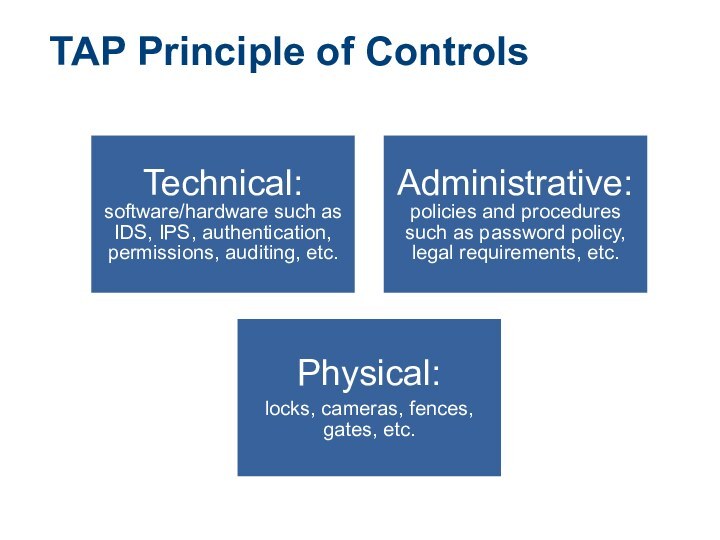
TAP Principle of Controls
Technical: software/hardware such as IDS,
IPS, authentication, permissions, auditing, etc.
Administrative: policies and procedures such
as password policy, legal requirements, etc. Physical:
locks, cameras, fences, gates, etc.
Слайд 6
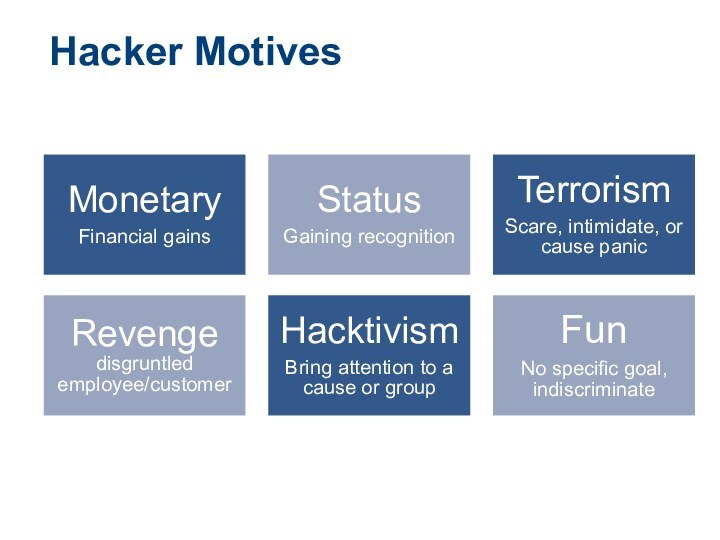
Hacker Motives
Monetary
Financial gains
Status
Gaining recognition
Terrorism
Scare, intimidate, or cause panic
Revenge
disgruntled
employee/customer
Hacktivism
Bring attention to a cause or group
Fun
No specific goal,
indiscriminate
Слайд 7
Common Attacks (1)
Theft of access: stealing passwords, subverting
access mechanisms to bypass normal authentication
Network intrusions: accessing a
system of computers without authorizationEmanation eavesdropping: intercepting radio frequency signals
Social engineering: telling lies to manipulate people into divulging information they otherwise would not provide
Posting and/or transmitting illegal material
Fraud: intentional deception to produce illegal financial gain or damage another party
Software piracy: violation of a license agreement, removing copy protection
Слайд 8
Common Attacks (2)
Dumpster diving: gathering discarded materials
Malicious
coding: software written to cause damage, destruction, or disruption;
viruses, worms, spyware, Trojan horsesDenial of service (DoS) and distributed DoS attacks: overloading a system’s resources not to provide required services
IP address spoofing: substituting a forged IP address for a valid address in network traffic or a message to disguise the true location of the message or person
Unauthorized destruction or alteration of information
Embezzlement: a financial fraud (theft, redirection of funds)
Data-diddling: unauthorized modification of data
Logic bomb: a piece of code designed to cause harm, intentionally inserted into software system
Слайд 9
Hacking as skillful modification of systems
Early Viruses, Phone
Phreaking
First Hacker Groups, Bulletin Boards
First Hacking Conference, Polymorphic Codes
in VirusesPre 1970
1970s
1980s
1990s
History of Hacking
Слайд 10
Famous Hacks over Time
1988 Robert T. Morris: the
first Internet worm
1999 David L. Smith: Melissa virus
2001 Jan
de Wit: Ana Kournikova virus2004 Adam Botbyl: steal credit card info
2005 Cameron Lacroix: hacking phone
Слайд 11
Famous Hackers and Groups
Individual Hackers:
Kevin Poulsen, Frank
Abagnale, Kevin Mitnick
Groups:
Black Hats:
The Cult of the
Dead Cow (cDc), Legion of DoomWhite Hats:
The Internet Storm Center, InfraGard
Слайд 12
Modern Hacking and Cybercriminals
Transformation of hobbyist hacking to
cybercrime
Cybercriminals seeking profits by aiming at financial data,
industry information, and other valuable targetsEmergence of national laws to counter cyber attacks
Слайд 13
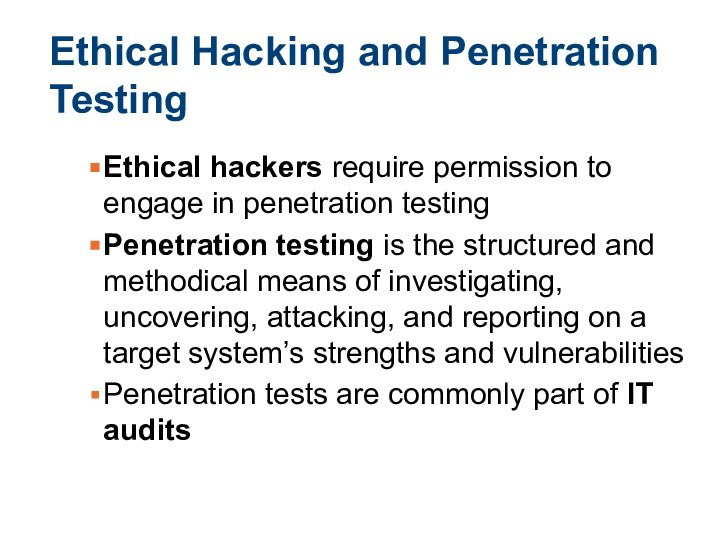
Ethical Hacking and Penetration Testing
Ethical hackers require permission
to engage in penetration testing
Penetration testing is the structured
and methodical means of investigating, uncovering, attacking, and reporting on a target system’s strengths and vulnerabilitiesPenetration tests are commonly part of IT audits
Слайд 14
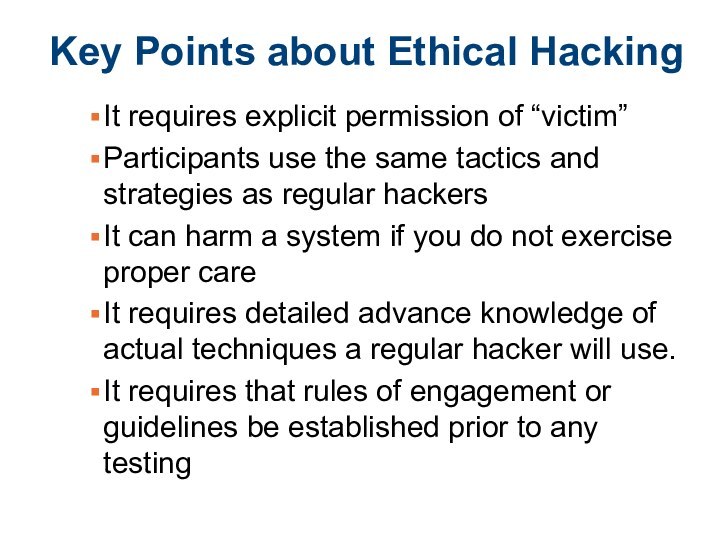
Key Points about Ethical Hacking
It requires explicit permission
of “victim”
Participants use the same tactics and strategies as
regular hackersIt can harm a system if you do not exercise proper care
It requires detailed advance knowledge of actual techniques a regular hacker will use.
It requires that rules of engagement or guidelines be established prior to any testing
Слайд 16
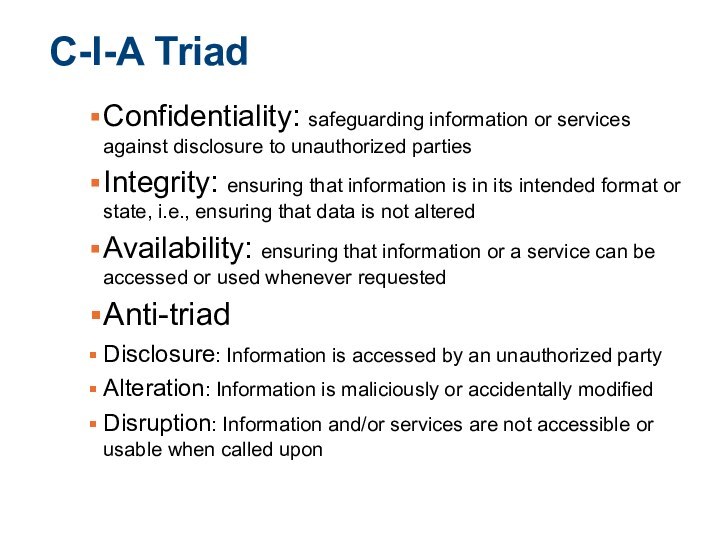
C-I-A Triad
Confidentiality: safeguarding information or services against disclosure
to unauthorized parties
Integrity: ensuring that information is in
its intended format or state, i.e., ensuring that data is not alteredAvailability: ensuring that information or a service can be accessed or used whenever requested
Anti-triad
Disclosure: Information is accessed by an unauthorized party
Alteration: Information is maliciously or accidentally modified
Disruption: Information and/or services are not accessible or usable when called upon
Слайд 18
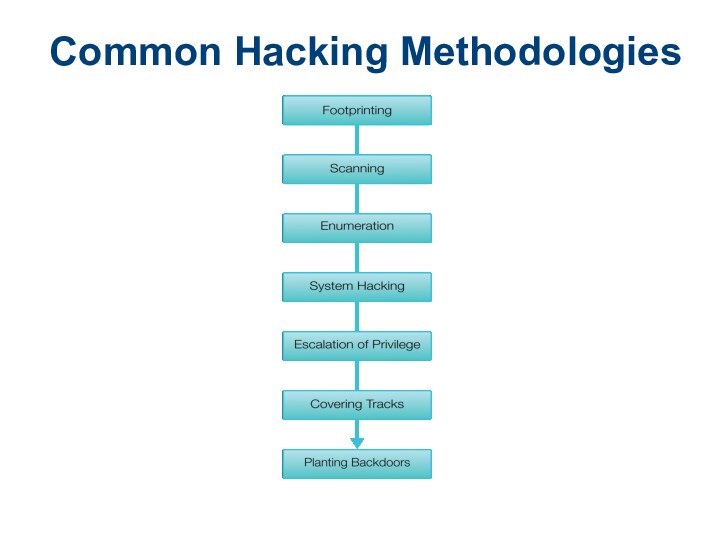
Hacking Methodologies
Footprinting: An attacker passively acquires information about
the intended victim’s system
Scanning: actively acquire more detailed information
about a victim; a ping sweep of all victim’s known IP addressed to see which machines respondEnumeration: extract more-detailed and useful information from a victim’s system
System hacking: actively attack a system
Escalation of privilege: obtains privileges on a given system higher than should be permissible
Covering tracks: purging information from the system to destroy evidence of a crime
Planting backdoors: for later use
Слайд 20
Performing a Penetration Test
Next logical step beyond ethical
hacking
Require rules to be agreed upon in advance
NIST 800-42
Guideline on network security testingTechnical attack
Administrative attack
Physical attack
Слайд 21
Laws and Ethical Standards
Ethical hackers should exercise proper
care not to violate the rules of engagement
When considering
breaking guidelinesTrust: questioning of other details
Legal action against ethical hacker
Regulations
Computer Fraud and Abuse Act
U.S. Communications Assistance for Law Enforcement Act
Sarbanes-Oxley Act (SOX)
Federal Information Security Management Act (FISMA)