- Главная
- Разное
- Бизнес и предпринимательство
- Образование
- Развлечения
- Государство
- Спорт
- Графика
- Культурология
- Еда и кулинария
- Лингвистика
- Религиоведение
- Черчение
- Физкультура
- ИЗО
- Психология
- Социология
- Английский язык
- Астрономия
- Алгебра
- Биология
- География
- Геометрия
- Детские презентации
- Информатика
- История
- Литература
- Маркетинг
- Математика
- Медицина
- Менеджмент
- Музыка
- МХК
- Немецкий язык
- ОБЖ
- Обществознание
- Окружающий мир
- Педагогика
- Русский язык
- Технология
- Физика
- Философия
- Химия
- Шаблоны, картинки для презентаций
- Экология
- Экономика
- Юриспруденция
Что такое findslide.org?
FindSlide.org - это сайт презентаций, докладов, шаблонов в формате PowerPoint.
Обратная связь
Email: Нажмите что бы посмотреть
Презентация на тему Hacking attacks
Содержание
- 2. Cyber crimeIn the start of 21 century,
- 3. HackingNowadays, a major concern that has emerged
- 4. Hacking For example, hacking mobile phones has become
- 5. HackingThere are four forms of attacks commonly
- 6. 1. Distributed Denial of Service (DDoS) attacksUsually
- 7. 2. Trojan HorseSoftware disguised as something else
- 8. 3. Virus Most commonPrimary concern is to
- 9. 4.WormA combination of a DDoS and a
- 10. What can hackers do?Steal services and/or valuable
- 11. BE CAREFUL!
- 12. Скачать презентацию
- 13. Похожие презентации
Cyber crimeIn the start of 21 century, the new era started. The era of technologies.However, with technologies, new types of crime developed.

Слайд 2
Cyber crime
In the start of 21 century, the
new era started. The era of technologies.
new types of crime developed.
Слайд 3
Hacking
Nowadays, a major concern that has emerged among
computer or smartphone users is the threat of hacking. Hackers
can easily hack the security systems, bank systems, any program and earn a lot of money.
Слайд 4
Hacking
For example, hacking mobile phones has become a
real business in Russia, Asia, and other places where
pre-paid phone calls are common. Analytics estimated that criminals, hackers who target mobile phones earn from $1000 to $5000 per day per person.
Слайд 5
Hacking
There are four forms of attacks commonly used
against computers and networks, according to Aaron Turpen, in
his article ‘Hacker Prevention Techniques.’
Слайд 6
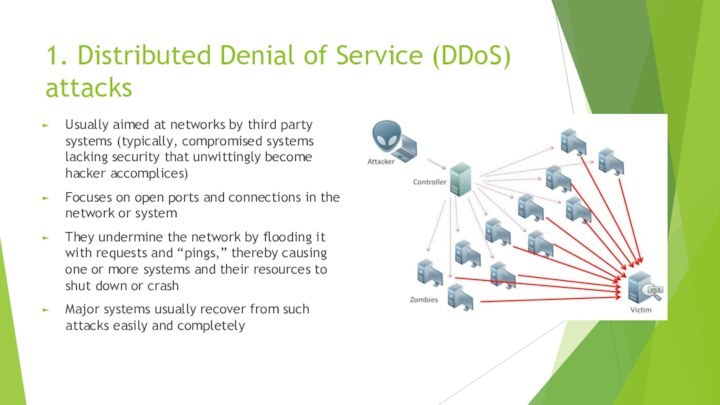
1. Distributed Denial of Service (DDoS) attacks
Usually aimed
at networks by third party systems (typically, compromised systems
lacking security that unwittingly become hacker accomplices)Focuses on open ports and connections in the network or system
They undermine the network by flooding it with requests and “pings,” thereby causing one or more systems and their resources to shut down or crash
Major systems usually recover from such attacks easily and completely
Слайд 7
2. Trojan Horse
Software disguised as something else (typically
useful shareware or freeware) and so are installed in
your system consciouslyIt either contains - a “back door,” (which allows others to enter your system, and do what they want with it, while you’re using the software), or - a “trigger,” (sets itself off when triggered, either by a date or a time or a series of events, etc., and cause your system to shut down or attack other computers; can be part of a DDoS attack
Difficult to detect
Слайд 8
3. Virus
Most common
Primary concern is to replicate and
spread itself, and then destroy or attempt an attack
on the host system
Слайд 9
4.Worm
A combination of a DDoS and a virus
attack
Usually reproduces as often as possible to spread as
widely as they canCommonly aimed at larger systems (mainframes, corporate networks, etc.); some are built to “consume” data and filter it back out to unauthorized users (i.e. corporate spies)
It consumes resources (quietly) until the system finally becomes overloaded and ceases to function
Слайд 10
What can hackers do?
Steal services and/or valuable files
Spy
on friends, family members or even business rivals
Steal your
money by using hacking techniques such as:- Setting up fake e-commerce sites to collect credit card details
Gaining entry to servers that contain credit card details